The Best AIOPS Platform for Accelerated Business Outcomes with ZIFTM
ZIFTM Documents
ZIF has an integrated automation module, which can resolve incidents in the IT process by automatically or manually triggering the bots.
Bots developed using any scripting language can be uploaded into ZIF and be re-used in workflows that can be created using ZIF. Workflow creator in ZIF is a low code component, that can be reused by the IT operations team.
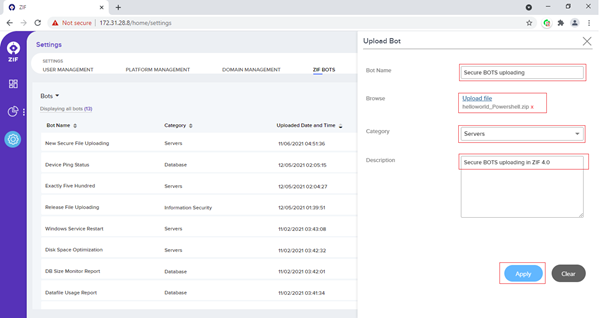
Uploading bots to ZIF:
In the settings, option navigate to ZIF Bots tab. Click on upload bot and enter the details of the bot in the sliding window that pop-ups and then click on apply.
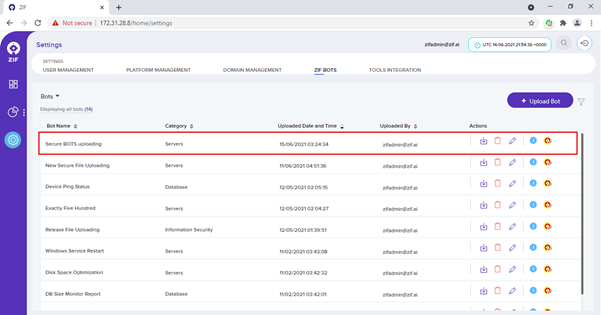
Once successfully uploaded the uploaded bot will be displayed in the bot details grid.
The below workflows are available in the platform that is used by the ITOps team. In the upcoming release, more workflows will be added to the platform.
| No. | Use Case | Category | Workflow Description |
| 1 | Windows Service Restart | Servers (Data Center) | Reads cases relevant to Service down alerts from ZIF A&P is used as input and automation workflow parses the target device information from A&P case and connects to the target device to start the service to running state if stopped. |
| 2 | CPU & Memory – Resource Utilization | Servers (Data Center) | Workflow polls the Incident from ITSM Tool at scheduled interval basis the defined filter criteria. It parses the ticket information to identify the device name and connects to the respective device to identify the top 5 CPU & Memory resource consuming processes. Incident is automatically closed when the resource utilization goes below the defined threshold value. |
| 3 | Java Application Restart | Application (Data Center) | Workflow connects to the target server at scheduled interval to restart Java application which are consuming high resource in terms of memory. |
| 4 | Log File Rotation | Servers (Data Center) | This automation workflow connects to the Linux Server to clean up the application & error logs on a periodic basis. It compresses the log files when the defined threshold level is met and deletes old log files from the system after the archival process. |
| 5 | Network printer Automation | End User Computing | Workflow gets the information logged in SR for the Network Printer request and perform action based on Add-Printer/Remove Printer. SR is automatically closed with appropriate journal notes at the end of remediation. |
| 6 | Ping Response Failure | Servers (Data Center) | Incidents are periodically checked in ITSM Tool basis the search parameters (Ex: Category => Monitoring, Subcategory => ZIF Monitor, Short Description => Host not responding) for Ping Failure alerts. Automation workflow connects to the target device logged in Incident and checks the device ping status for reachability. Incident status is updated accordingly in ITSM Tool along with work notes based on device reachability. |
| 7 | IIS Application Pool Monitoring | Application (Data Center) | Workflow automates to start the Application Pool when a pool is found to be stopped or crashed in IIS Server. Also monitors the availability and health status of different Application Pools configured in IIS Server. |
| 8 | Suppress CPU/Memory Alerts Automation | Hyper Automation | Replace the manual efforts involved in monitoring the backup/antivirus scan/database/application critical processes and suppress those high resource usage alerts as part of this automation. Create/Escalate incident to Windows/Linux Server Team through Monitoring Tool alerts in case of consistent high resource utilization basis the process name, hours of running and automatically closes the incident incase of decrease in resource spike. |
| 9 | Windows Process Kill | Servers (Data Center) | This workflow monitors periodically on defined list of servers for critical processes for application availability and automatically kills the topmost CPU & memory resource consuming process. Details of killed process is shared with respective DL via email at the end of remediation. |
| 10 | Make an inactive user in AD to an active user Automation | End User Computing | ITSM Tickets are polled at regular intervals for Employee Rehire Automation. User account is enabled again in Active Directory based on the user information (Ex: Username, Email Address, Employee ID) logged in the request. SR is closed with appropriate work notes after enabling the account in AD. |
| 11 | AD User Account Extension | End User Computing | Tickets are periodically checked in ITSM Tool for User Account Extension Request. Account Expiry date is extended in Active Directory for specific user based on the information (Ex: Username, Email Address, Employee ID) reported in ITSM Tool. SR is closed automatically with appropriate journal notes after updating the user account. |
| 12 | Employee Onboarding | Identity & Access Management | Tickets are periodically checked in ITSM Tool for Employee onboarding requests. Gets the key attributes of user from the SR and creates a user account in Active Directory as part of Employee Onboarding Automation. User is also mapped with respective Security Group based on attributes mapping (Position, Office Location, Country, Business Unit). Ticket is automatically closed with appropriate journal notes and email notification to HR/IT/Admin personnel at the end of remediation. |
| 13 | Automated Execution of Ansible Playbook | Servers (Data Center) | Helps to automate IT infrastructure, Configuration Management, Application Deployment and Software/Package Installation in target machines using Ansible Playbooks. At the end of remediation, automation generates the consolidated result and sends the report to mailing group. (Example: No. of devices succeeded/failed with package installation through this automation) |
| 14 | Apache Process Kill | Application (Data Center) | ZIF Remediation Engine establishes connection with the targeted device to identify the high consuming Apache process in terms of resource utilization and kills the Apache process with top memory consumption |
| 15 | Automated Problem Ticket Creation | Hyper Automation | Creation of Problem Ticket in ITSM Tool when more alerts are generated for a particular device in the last 48 – 72 hours (which is configurable). Ticket includes all the alert identifiers for that device in description/journal notes and assigns it to Resolver Group for their action. |
| 16 | DL Management Automation with ServiceNow | End User Computing | Request gets processed by this Workflow based on SR raised in ITSM Tool for DL Management. User is added as a member of specific DL or removed from DL membership as a part of this remediation. SR gets automatically closed with appropriate work notes. |
| 17 | Hyper-V VM Automation | Servers (Data Center) | Automates the shutdown of VMs at specific slot for maintenance, backups, updates or recover process. It brings back the VM in running mode after the maintenance window slot or Ad-hoc basis through ticket request. |
| 18 | URL Verdict Report | SIEM & Security Management | Observable such as suspicious/phishing URL is parsed from ITSM Incident and scanned for verdict score using Threat Intelligence Tool. Verdict Analysis Report is shared as an email in HTML format with Security Operations Team for blocking the URL in Content Filtering Tool or Firewall based on threat score. |
| 19 | Windows Log Monitoring | Ad-hoc Monitoring | Workflow periodically connects to the respective Windows device and monitors the log file for defined error/key patterns. It raises an email alarm to mailing group when such error pattern is reported in the log file. |
| 20 | Linux Log Monitoring | Ad-hoc Monitoring | Workflow periodically connects to the respective Unix/Linux device and monitors the log file for defined error/key patterns. It raises an email alarm to mailing group when such pattern is reported in the log file. |
| 21 | EDI Monitoring – Reporting of Stuck File | Ad-hoc Monitoring | Monitors the targeted folders in respective server for stuck file reporting based on the file count, age of file, folder/file patterns as part of EDI application monitoring. Reports an incident in ITSM Tool when any stuck file is identified basis the defined monitoring parameters and triggers an email notification to respective mailing group |
| 22 | NFS Space Availability | Ad-hoc monitoring | Monitors the space left on mounted NFS device at regular intervals. It generates an incident in ITSM Tool when the space availability is found higher than the defined threshold level. |
| 23 | Correalated Case/Alert Closure Automation | Hyper Automation | Reads open cases basis the timeframe and closes the cases along with associated alerts in ZIF A&P module. It acts like Tech Bot to identify the open cases (> no. of days) and reports an email alert to DL with closed cases. |
Fill in your details, our sales team will get in touch to schedule the demo.